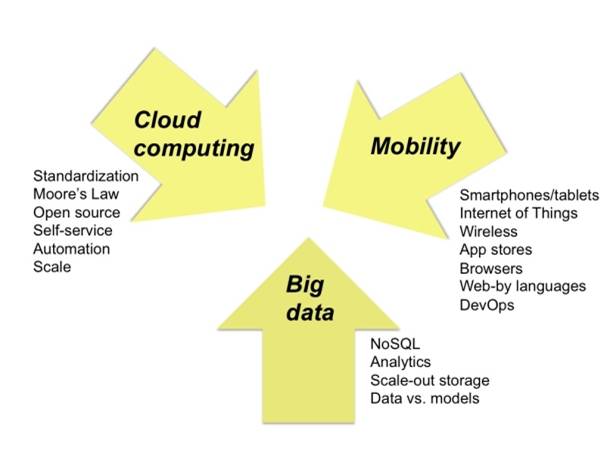
Predicting the future of any market is not easy by any stretch of imagination, many parameters are involved in the process, but understanding the near past, the existing patterns, and then using those patterns to pick the likely direction of the market is one way to do it. This applies to the big 3 in Tech world: Cloud Computing, Big Data and Mobility (CBM), they are controlling the future of the Tech market, and just to understand the magnitude and size of the market, take for example the case of big data and analytics market, it will reach $125 billion worldwide in 2015, according to IDC.
The fuel of the massive growth of big data and analytics in 2015 is a new trend of less focus on collecting everything and anything and more about focusing on the most relevant data for actionable insights. More organizations will also look at how machine generated data can add value to their business, not just data coming from customers or employees, according to analysts.
As the Internet of Things and wearable devices take off, there is going to be more machine generated data for organizations to tap into. More organizations next year will assess the opportunities and value of that data, as well as how they can mash it with the human generated data to get as much insight as they can. In other words, Big Data will become Smart Data.
Cloud computing will go the way of the big 3 in auto industry with more reconciliation and mergers / acquisitions , we will end up with few big names dominating the market namely Google, Amazon, IBM, Microsoft. The general direction will be towards hybrid cloud option over pure public or privet cloud.
Mobility will see more of cooperation and alliances between companies on the far ends of the spectrum of technology ecosystem; a prime example is IBM and Apple partnership using the devices of Apple with the enterprise technology of IBM.
Technology Trends in 2015
David Cearley is vice president and Gartner Fellow listed three main themes with 2015 tech trends: merging of the real and virtual worlds, technology impact of the digital business shif and intelligence everywhere.
Computing Everywhere
As mobile devices continue to proliferate, Gartner predicts an increased emphasis on serving the needs of the mobile user in diverse contexts and environments, as opposed to focusing on devices alone.
The Internet of Things
The combination of data streams and services created by digitizing everything creates four basic usage models: manage, monetize, operate and extend.
These four basic models can be applied to any of the four “Internets.” Enterprises should not limit themselves to thinking that only the Internet of Things (IoT) (assets and machines) has the potential to leverage these four models. For example, the pay-per-use model can be applied to assets (such as industrial equipment), services (such as pay-as-you-drive insurance), people (such as movers), places (such as parking spots) and systems (such as cloud services). Enterprises from all industries can leverage these four models.
Advanced, Pervasive and Invisible Analytics
Analytics will take center stage as the volume of data generated by embedded systems increases and vast pools of structured and unstructured data inside and outside the enterprise are analyzed. “Every app now needs to be an analytic app,” said Mr. Cearley. “Organizations need to manage how best to filter the huge amounts of data coming from the IoT, social media and wearable devices, and then deliver exactly the right information to the right person, at the right time. Analytics will become deeply, but invisibly embedded everywhere.” Big data remains an important enabler for this trend but the focus needs to shift to thinking about big questions and big answers first and big data second — the value is in the answers, not the data.
Context-Rich Systems
Ubiquitous embedded intelligence combined with pervasive analytics will drive the development of systems that are alert to their surroundings and able to respond appropriately. Context-aware security is an early application of this new capability, but others will emerge. By understanding the context of a user request, applications can not only adjust their security response but also adjust how information is delivered to the user, greatly simplifying an increasingly complex computing world. Rich media analytics will at least triple in 2015 and emerge as the key driver for big data technology investment. Already half of large organizations in North America are reporting use of rich media (video, audio, image) data as part of their big data analytics projects, and all large organizations will analyze rich media in five years. (IDC)
Security at the App-Level
All roads to the digital future lead through security. However, in a digital business world, security cannot be a roadblock that stops all progress. Organizations will increasingly recognize that it is not possible to provide a 100 percent secured environment. Once organizations acknowledge that, they can begin to apply more-sophisticated risk assessment and mitigation tools. On the technical side, recognition that perimeter defense is inadequate and applications need to take a more active role in security gives rise to a new multifaceted approach. Security-aware application design, dynamic and static application security testing, and runtime application self-protection combined with active context-aware and adaptive access controls are all needed in today’s dangerous digital world. This will lead to new models of building security directly into applications. Perimeters and firewalls are no longer enough; every app needs to be self-aware and self-protecting.
Security at the System-Level
Big data analytics tools will be the first line of defense, combining machine learning, text mining and ontology modeling to provide holistic and integrated security threat prediction, detection, and deterrence and prevention programs. Forrester analyst, Tim Sheedy, pointed out the potential increase in attacks or privacy breaches in 2015 that coincide with the uptake in devices generating data. “I believe we will see an accelerated rate of organizations having security issues or challenges, whether they are hacks, or privacy issues, over the next 12 months,” Sheedy said.
Big Data as a Service
Big data as a service (BDaaS) is a term typically used to refer to services that offer analysis of large or complex data sets, using the cloud hosted services. Similar types of services include software as a service (SaaS) or infrastructure as a service (IaaS), where specific big data as a service options are used to help businesses handle what the IT world calls big data or sophisticated aggregated data sets that provide a lot of value for today’s companies.
Mobile Cloud Computing (Cloud/Client)
Mobile cloud computing is a technique or model in which mobile applications are built, powered and hosted using cloud computing technology. A mobile cloud approach enables developers to build applications designed specifically for mobile users without being bound by the mobile operating system and the computing or memory capacity of the smartphone. Mobile cloud computing apps are generally accessed via a mobile browser from a remote webserver, typically without the need for installing a client application on the recipient phone.
The convergence of cloud and mobile computing will continue to promote the growth of centrally coordinated applications that can be delivered to any device. “Cloud is the new style of elastically scalable, self-service computing, and both internal applications and external applications will be built on this new style,” said Mr. Cearley.
“While network and bandwidth costs may continue to favor apps that use the intelligence and storage of the client device effectively, coordination and management will be based in the cloud.”
In the near term, the focus for cloud/client will be on synchronizing content and application state across multiple devices and addressing application portability across devices. Over time, applications will evolve to support simultaneous use of multiple devices. The second-screen phenomenon today focuses on coordinating television viewing with use of a mobile device. In the future, games and enterprise applications alike will use multiple screens and exploit wearables and other devices to deliver an enhanced experience.
Software-Defined Applications and Infrastructure
Agile programming of everything from applications to basic infrastructure is essential to enable organizations to deliver the flexibility required to make the digital business work. Software-defined networking, storage, data centers and security are maturing. Cloud services are software-configurable through API calls, and applications, too, increasingly have rich APIs to access their function and content programmatically. To deal with the rapidly changing demands of digital business and scale systems up — or down — rapidly, computing has to move away from static to dynamic models. Rules, models and code that can dynamically assemble and configure all of the elements needed from the network through the application are needed.
Few Major Players in the Cloud
There will be more market convergence around the major public cloud computing players; Google, AWS, IBM, and Microsoft. Enterprises moving to public cloud are investing in these companies’ products. Moreover, cloud computing is where these big players are placing their technology bets right now and this will occur for the foreseeable future.
Ahmed Banafa, Author the Books:
Secure and Smart Internet of Things (IoT) Using Blockchain and AI
Blockchain Technology and Applications
References:
http://www.forbes.com/sites/gilpress/2014/12/11/6-predictions-for-the-125-billion-big-data-analytics-market-in-2015/2/
http://www.gartner.com/newsroom/id/2867917
http://www.cio.com.au/article/559668/where-big-data-analytics-heading-2015/
http://www.computerworld.com/article/2851517/network-security-needs-big-data.html
https://www.linkedin.com/pulse/20140629041128-246665791-big-data-as-a-service-the-next-big-thing?trk=object-title
https://www.linkedin.com/pulse/20140322222940-246665791-the-third-platform-mobile-cloud-computing-mcc?trk=mp-reader-card
Comments on this publication