The Internet of Things (IoT) phenomenon—ubiquitous connected things providing key physical data and further processing of that data in the cloud to deliver business insights— presents a huge opportunity for many players in all businesses and industries. Many companies are organizing themselves to focus on IoT and the connectivity of their future products and services.
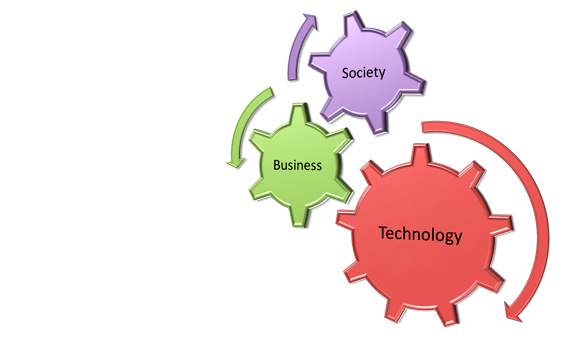
For the IoT industry to thrive there are three categories of challenges to overcome and this is true for any new trend in technology not only IoT:
- Technology
- Business
- Society
Technology
This part is covering all the technologies needed to make IoT systems function smoothly as a standalone solution or part of existing systems. Cloud Security Alliance (CSA) listed some of the root causes of such technological challenges:
- Many IoT Systems are poorly designed and implemented, using diverse protocols and technologies that create complex configurations.
- Lack of mature IoT technologies and business processes.
- Limited guidance for life cycle maintenance and management of IoT devices.
- Limited best practices available for IoT developers.
- There is a lack of standards for authentication and authorization of IoT edge devices.
- There are no best practices for IoT-based incident response activities.
- Audit and Logging standards are not defined for IoT components.
- Restricted interfaces available IoT devices to interact with security devices and applications.
- No focus yet on identifying methods for achieving situational awareness of the security posture of an organization’s IoT assets.
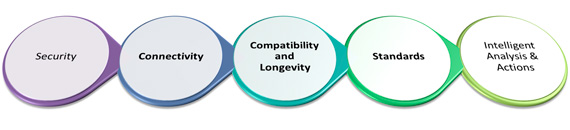
Security
IoT has already turned into a serious security concern that has drawn the attention of prominent tech firms and government agencies across the world. The hacking of baby monitors, smart fridges, thermostats, drug infusion pumps, cameras and even assault rifles are signifying a security nightmare being caused by the future of IoT. So many new nodes being added to networks and the internet will provide malicious actors with innumerable attack vectors and possibilities to carry out their evil deeds, especially since a considerable number of them suffer from security holes.
This fear was realized with a massive distributed denial of service attack that crippled the servers of services like Twitter, NetFlix , NYTimes, and PayPal across the U.S. on October 21st , 2016. It’s the result of an immense assault that involved millions of Internet addresses and malicious software, according to Dyn, the prime victim of that attack. “One source of the traffic for the attacks was devices infected by the Mirai botnet” the link to the source code of Mirai malware on GitHub is here. The attack comes amid heightened cybersecurity fears and a rising number of Internet security breaches. Preliminary indications suggested that countless Internet of Things (IoT) devices that power everyday technology like closed-circuit cameras and smart-home devices were hijacked by the malware, and used against the servers.
The more important shift in security will come from the fact that IoT will become more ingrained in our lives. Concerns will no longer be limited to the protection of sensitive information and assets. Our very lives and health can become the target of IoT hack attacks.
There are many reasons behind the state of insecurity in IoT. Some of it has to do with the industry being in its “gold rush” state, where every vendor is hastily seeking to dish out the next innovative connected gadget before competitors do. Under such circumstances, functionality becomes the main focus and security takes a back seat.
Connectivity
Connecting so many devices will be one of the biggest challenges of the future of IoT, and it will defy the very structure of current communication models and the underlying technologies. At present we rely on the centralized, server/client paradigm to authenticate, authorize and connect different nodes in a network.
This model is sufficient for current IoT ecosystems, where tens, hundreds or even thousands of devices are involved. But when networks grow to join billions and hundreds of billions of devices, centralized brokered systems will turn into a bottleneck. Such systems will require huge investments and spending in maintaining cloud servers that can handle such large amounts of information exchange, and entire systems can go down if the server becomes unavailable.
The future of IoT will very much have to depend on decentralizing IoT networks. Part of it can become possible by moving functionality to the edge, such as using fog computing models where smart devices such as IoT hubs take charge of time-critical operations and cloud servers take on data gathering and analytical responsibilities.
Other solutions involve the use of peer-to-peer communications, where devices identify and authenticate each other directly and exchange information without the involvement of a broker. Networks will be created in meshes with no single point of failure. This model will have its own set of challenges, especially from a security perspective, but these challenges can be met with some of the emerging IoT technologies such as Blockchain.
Compatibility and Longevity
IoT is growing in many different directions, with many different technologies competing to become the standard. This will cause difficulties and require the deployment of extra hardware and software when connecting devices.
Other compatibility issues stem from non-unified cloud services, lack of standardized M2M protocols and diversities in firmware and operating systems among IoT devices.
Some of these technologies will eventually become obsolete in the next few years, effectively rendering the devices implementing them useless. This is especially important, since in contrast to generic computing devices which have a lifespan of a few years, IoT appliances (such as smart fridges or TVs) tend to remain in service for much longer, and should be able to function even if their manufacturer goes out of service.
Standards
Technology standards which include network protocols, communication protocols, and data-aggregation standards, are the sum of all activities of handling, processing and storing the data collected from the sensors. This aggregation increases the value of data by increasing, the scale, scope, and frequency of data available for analysis.
Challenges facing the adoptions of standards within IoT
- Standard for handling unstructured data: Structured data are stored in relational databases and queried through SQL for example. Unstructured data are stored in different types of NoSQL databases without a standard querying approach.
- Technical skills to leverage newer aggregation tools: Companies that are keen on leveraging big-data tools often face a shortage of talent to plan, execute, and maintain systems.
Intelligent Analysis & Actions
The last stage in IoT implementation is extracting insights from data for analysis, where analysis is driven by cognitive technologies and the accompanying models that facilitate the use of cognitive technologies.
Factors driving adoption intelligent analytics within the IoT;
- Artificial intelligence models can be improved with large data sets that are more readily available than ever before, thanks to the lower storage.
- Growth in crowdsourcing and open- source analytics software: Cloud-based crowdsourcing services are leading to new algorithms and improvements in existing ones at an unprecedented rate.
- Real-time data processing and analysis: Analytics tools such as complex event processing (CEP) enable processing and analysis of data on a real-time or a near real-time basis, driving timely decision making and action.
Challenges facing the adoptions of intelligent analytics within IoT
- Inaccurate analysis due to flaws in the data and/or model: A lack of data or presence of outliers may lead to false positives or false negatives, thus exposing various algorithmic limitations
- Legacy systems’ ability to analyze unstructured data: Legacy systems are well suited to handle structured data; unfortunately, most IoT/business interactions generate unstructured data
- Legacy systems’ ability to manage real- time data: Traditional analytics software generally works on batch-oriented processing, wherein all the data are loaded in a batch and then analyzed
The second phase of this stage is intelligent actions which can be expressed as M2M and M2H interfaces for example with all the advancement in UI and UX technologies.
Factors driving adoption of intelligent actions within the IoT
- Lower machine prices.
- Improved machine functionality.
- Machines “influencing” human actions through behavioral-science rationale.
- Deep Learning tools.
Challenges facing the adoption of intelligent actions within IoT
- Machines’ actions in unpredictable situations.
- Information security and privacy.
- Machine interoperability.
- Mean-reverting human behaviors.
- Slow adoption of new technologies.
Business
The bottom line is a big motivation for starting, investing in, and operating any business, without a sound and solid business model for IoT we will have another bubble , this model must satisfy all the requirements for all kinds of e-commerce; vertical markets, horizontal markets, and consumer markets. But this category is always a victim of regulatory and legal scrutiny.
End-to-end solution providers operating in vertical industries and delivering services using cloud analytics will be the most successful at monetizing a large portion of the value in IoT. While many IoT applications may attract modest revenue, some can attract more. For little burden on the existing communication infrastructure, operators have the potential to open up a significant source of new revenue using IoT technologies.
Clearly, it is important to understand the value chain and business model for the IoT applications for each category of IoT.
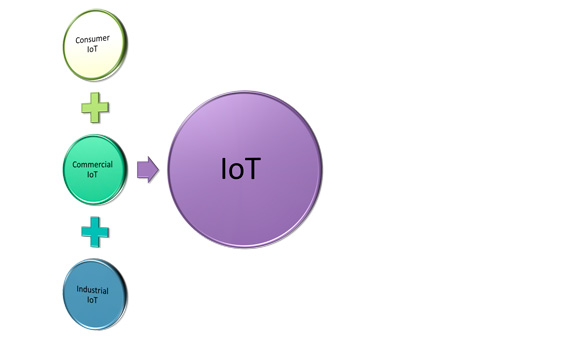
IoT can be divided into 3 categories based on usage and clients base:
- Consumer IoT includes the connected devices such as smart cars, phones, watches, laptops, connected appliances, and entertainment systems.
- Commercial IoT includes things like inventory controls, device trackers, and connected medical devices.
- Industrial IoT covers such things as connected electric meters, waste water systems, flow gauges, pipeline monitors, manufacturing robots, and other types of connected industrial devices and systems.
Society
Understanding IoT from the customers and regulators prospective is not an easy task for the following reasons:
- Customer demands and requirements change constantly.
- New uses for devices—as well as new devices—sprout and grows at breakneck speeds.
- Inventing and reintegrating must-have features and capabilities are expensive and take time and resources.
- The uses for Internet of Things technology are expanding and changing—often in uncharted waters.
- Consumer Confidence: Each of these problems could put a dent in consumers’ desire to purchase connected products, which would prevent the IoT from fulfilling its true potential.
- Lack of understanding or education by consumers of best practices for IoT devices security to help in improving privacy, for example change default passwords of IoT devices.
Social and Legal Challenges and Privacy
The IoT creates unique challenges to privacy, many that go beyond the data privacy issues that currently exist. Much of this stems from integrating devices into our environments without us consciously using them.
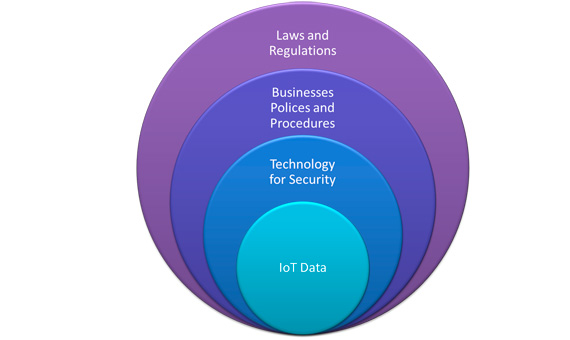
This is becoming more prevalent in consumer devices, such as tracking devices for phones and cars as well as smart televisions. In terms of the latter, voice recognition or vision features are being integrated that can continuously listen to conversations or watch for activity and selectively transmit that data to a cloud service for processing, which sometimes includes a third party. The collection of this information exposes legal and regulatory challenges facing data protection and privacy law.
In addition, many IoT scenarios involve device deployments and data collection activities with multinational or global scope that cross social and cultural boundaries. What will that mean for the development of a broadly applicable privacy protection model for the IoT?
In order to realize the opportunities of the IoT, strategies will need to be developed to respect individual privacy choices across a broad spectrum of expectations, while still fostering innovation in new technologies and services.
Regulatory Standards
Regulatory standards for data markets are missing especially for data brokers; they are companies that sell data collected from various sources. Even though data appear to be the currency of the IoT, there is a lack of transparency about; who gets access to data and how those data are used to develop products or services and sold to advertisers and third parties. There is a need for clear guidelines on the retention, use, and security of the data including metadata (the data that describe other data).
Ahmed Banafa
Faculty | Author | Speaker| 5-time instructor of the year
References:
http://www.microwavejournal.com/articles/27690-addressing-the-challenges-facing-iot-adoption
https://www.linkedin.com/pulse/wake-up-call-iot-ahmed-banafa?trk=mp-author-card
https://www.linkedin.com/pulse/iot-implementation-challenges-ahmed-banafa?trk=mp-author-card
https://www.linkedin.com/pulse/why-iot-needs-fog-computing-ahmed-banafa?trk=mp-author-card
Diagrams Credit: Ahmed Banafa
Comments on this publication