In 1547, the Holy Roman Emperor Charles V—known as Charles I in Spain and Austria—sent a coded letter to Jean de Saint-Mauris, his ambassador to the French court, entrusting him with a secret message. Apart from the addressee of the letter, and probably the spies and cryptanalysts working for the French monarch, Francis I, and therefore also the Gallic king, nobody else would have had access to the information contained in the mysterious letter, which is now kept in Stanislas Library in Nancy (France). Nobody, that is, until now.
The investigation
It was a team of researchers, led by the French cryptographer Cecile Pierrot, a research fellow at Inria (the French National Institute for Research in Digital Science and Technology), who finally managed to crack the Emperor’s code after six months of intense work. After trying in vain on her own, Pierrot recruited two colleagues—an expert in complex analysis and a computer scientist with expertise in algorithmic logic. Together they formulated several hypotheses in the form of custom-made algorithms, which they then tested with the help of powerful computers. But even then, they were unable to crack the enigmatic code. They had no choice but to enlist the help of Camille Desenclos, a historian and expert in the political intricacies and cryptographic systems of the time, to find a clue or historical reference that would give them access to Charles V’s cipher.
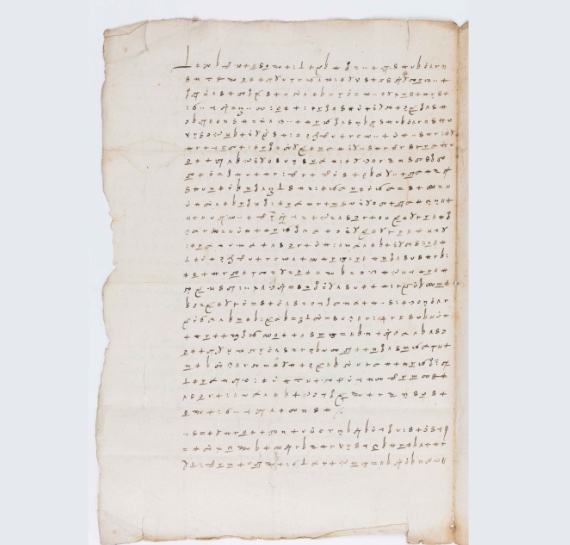
In the end, it was Desenclos who found the definitive clue by investigating Saint-Mauris’s surviving correspondence and discovering another letter written with the same cipher system with transcribed fragments noted in the margins. Armed with their own Rosetta Stone, the French cryptanalysts were finally able to decipher the code and establish that the Emperor’s message confided to his ambassador his suspicions that Francis I was plotting to assassinate him and urged him to investigate.
The cipher
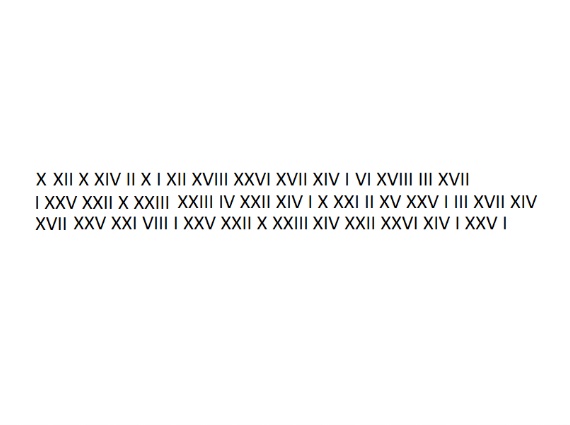
The Emperor’s cipher—presumably devised by the expert cryptographers of the Imperial Chancery—consisted of a nomenclator, or code sheet. This coding system is based on a cipher alphabet, which is used to encode most of the message, and is complemented by a list of coded words and other symbols with a specific meaning, as can be seen in the following diagram, which was shown by Cecile Pierrot during the presentation of her results:
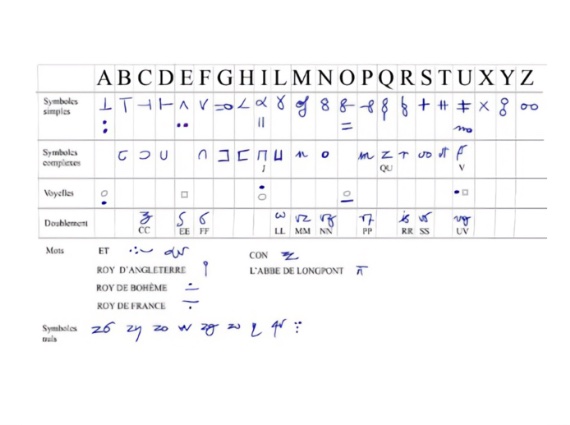
The complexity of the royal code lies in the fact that it combines two sets of symbols (simple and complex) to represent the different letters of the alphabet, depending on how they are integrated into words. Thus, when a consonant is followed by a vowel, it is represented by the corresponding complex symbol, with the diacritical mark representing that vowel. With the added difficulty that, in this case, since the letter E has no associated diacritical mark, any Es in the message following a consonant disappear or are omitted. Simple symbols are used for vowels when they are the first letter of the word or when they follow another vowel, and for consonants when they are not immediately followed by another vowel.
The code also contains meaningless symbols and others representing important political figures who would be expected to be mentioned in a message sent or forwarded to a high-ranking official. All this was designed to make cryptanalysis more difficult.
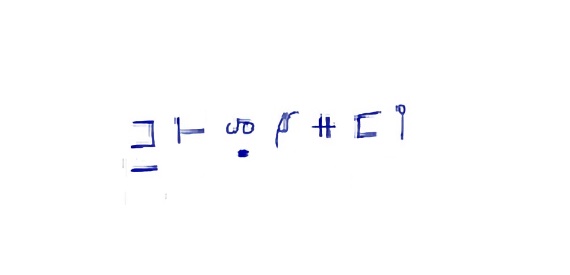
Brainteaser 1: A royal message
Using the nomenclator on which the Charles V code is based, deciphering the following message should be child’s play.
The cryptographic connection between Charles V and Mary Stuart
A very similar nomenclator was also used by Mary Stuart, Queen of Scots, to communicate with her followers in her confrontation with Queen Elizabeth I, which would ultimately lead to her execution.
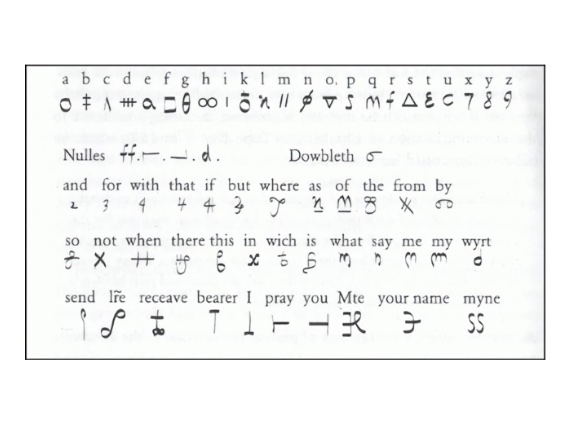
Brainteaser 2: Another inquisitive secret message to Ambassador Saint-Mauris

But this is neither the only nor the most tragic cryptographic link between the Spanish Crown and Mary Stuart. Charles I’s successor, Philip II, also used ciphers in his correspondence with his half-brother, John of Austria. At least one of these letters, describing a plan to invade England, was intercepted by William the Silent’s spies and deciphered by his chief cryptanalyst, Philips of Marnix. William shared the plan with his English allies, which largely convinced the English Minister of Defence of the need to create a “cipher school”—the forerunner of today’s British GCHQ (Government Communications Headquarters) and so many other national intelligence agencies. The linguist Thomas Phelippes was appointed secretary of the school and was soon to be responsible for deciphering Mary Stuart’s nomenclator and thereby exposing her conspiracy plans, for which she was condemned to death: on 8 February 1587, she was beheaded in the Great Hall of Fotheringhay Castle.
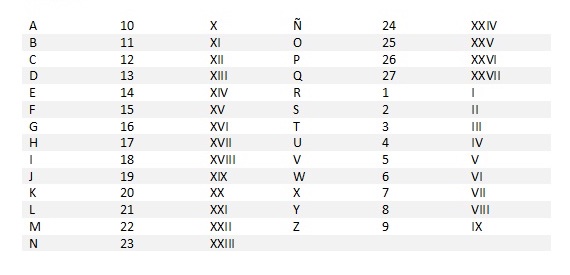
Brainteaser 3: A cipher based on Xs, Is and Vs
Now that you are an expert in Charles V’s cipher, the challenge is presented as a secret message encoded with an original cipher that pays homage to Emperor Charles V.
The message:
Solutions
Miguel Barral
Comments on this publication